
Six Critical Actions for Security Leaders in Faith‑Based Schools and Executive Protection Programs
Security professionals often prepare for the threats they see most frequently: disruptive individuals, protest activity, workplace violence, or opportunistic crime.
However, global tensions and ideological conflicts increasingly produce a different category of risk. These threats may emerge quietly and without warning from individuals who have lived and operated within communities for extended periods before acting.
Often referred to as 'sleeper‑style threats,' these actors may remain dormant for years while blending into normal life before being directed or inspired to carry out violence or disruption.
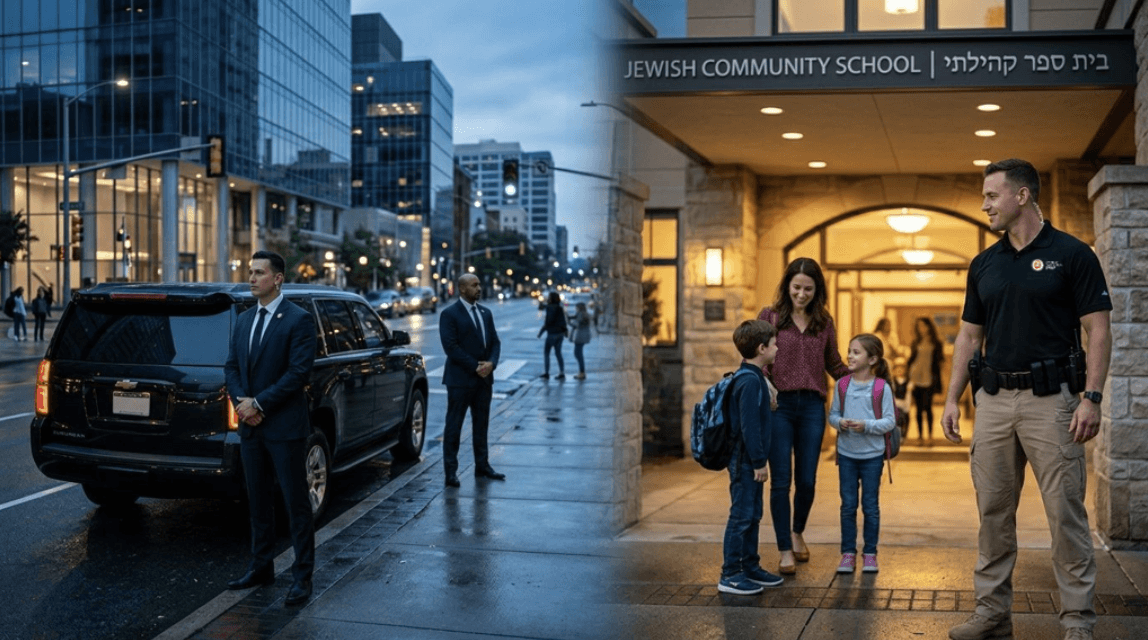
For faith‑based schools, houses of worship, and high‑profile executives, the implications are significant. These environments are often considered symbolic targets due to their visibility, values, or perceived influence.
Security leaders responsible for protecting these communities must therefore think beyond traditional threats and ensure their programs are prepared for complex, coordinated incidents.
1. Strengthen Community Awareness and Reporting
Early detection of concerning behavior rarely begins with technology or intelligence systems.
More often, it starts with observant people noticing something unusual.
Faith‑based schools and community organizations should cultivate a culture where staff, congregants, parents, and volunteers feel comfortable reporting suspicious behavior.
Key practices include situational awareness training, clear reporting pathways, anonymous reporting options when appropriate, and coordination with local law enforcement.
2. Train for Coordinated or Multi‑Location Incidents
Many organizations still train primarily for single‑actor incidents. Modern attacks may involve multiple actors, multiple locations, diversion tactics, or coordinated timing.
Training exercises should include complex scenarios such as simultaneous incidents at separate buildings, medical emergencies during a security event, and evacuation and reunification challenges.
3. Build Strong Intelligence and Information‑Sharing Relationships
Private security teams do not operate in isolation.
Effective protection requires close relationships with law enforcement agencies, FBI Joint Terrorism Task Forces, fusion centers, and community security organizations.
For executive protection teams, partnerships may also include corporate security departments, protective intelligence analysts, and international security partners.
4. Harden Soft Targets Without Disrupting Community Life
Faith‑based schools and community institutions are often designed to be welcoming rather than fortified.
Security programs should balance openness with practical measures such as access control, visitor management, surveillance coverage of entrances, controlled drop‑off procedures, and clearly defined lockdown protocols.
5. Incorporate Emerging Threats into Risk Assessments
Threats evolve rapidly and security programs must remain aware of emerging risks such as drone reconnaissance, encrypted communications used to coordinate activity, and remote direction of attacks.
Protective intelligence programs should regularly update risk assessments and adapt security protocols accordingly.
6. Adopt a 'Think Globally, Act Locally' Security Mindset
International conflicts can produce ripple effects far from the original battlefield.
Organizations must recognize that global political or ideological tensions may increase risks for religious communities, prominent corporate leaders, and symbolic institutions.
Leadership Matters
Preparedness is not about alarmism. It is about responsible stewardship of the people and communities entrusted to our care.
For faith‑based institutions and executive protection teams alike, the question is not whether threats evolve. They always do.
The real question is whether security programs evolve with them.
Strong partnerships, proactive planning, and well‑trained personnel remain the most effective defense against threats that seek to exploit complacency.





